Tag: device
Areas Digital Forensic Investigators Find Evidence
[Abstract] The purpose of this document is to provide a basic understanding of computer forensics by identifying five areas in computers and computer applications a forensic investigator can look for digital evidence. Also included within this document are three types of criminal investigations that can utilize the services of computer forensic investigators. Lastly, a description …
Link and End-to-End Encryption Techniques
Abstract The purpose of this document is to provide fundamental differences between link and end-to-end encryption techniques. Also included within this document is a description of traffic padding and what its fundamental purpose is. The last item that can be found within this document is a description of differences between a session key and a …
Network Testing Programs
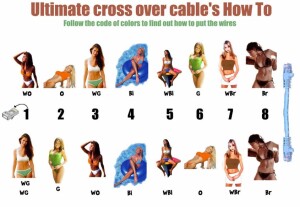
[Abstract] The purpose of this document is to explain different types of testing programs that can be used to identify network latency issues when planning a network upgrade. Also included within this document are naming conventions for networking devices and hosts. Lastly this document will outline and explain different types of equipment and their roles …
Networking Protocols and Models
[Abstract] The purpose of this document is to explain different networking protocols and models by explaining what is needed to upgrade a network from a bus topology to a star topology. Also included within this document is information about a network design to allow for maximum users with maximum throughput for 100Mbps to the customer’s …
Information Systems and Users
[Abstract] The purpose of this document is to provide an increased or basic knowledge of how users interact with information systems by utilizing input and output devices, computer performance factors, network performance issues, and correlating them to the online virtual campus. [Content] When viewing the American Intercontinental University online virtual campus system as an information …
Stun Gun
Pocket Taser Stun Gun, a great gift for the wife. A guy who purchased his lovely wife a pocket Taser for their anniversary submitted this : Last weekend I saw something at Larry’s Pistol & Pawn Shop that sparked my interest. The occasion was our 22nd anniversary and I was looking for a little something …
Advantages and Disadvantages of Network Topologies
Different network topologies have different advantages and disadvantages. A bus network topology is nice because it is simple and cheap, however it has its limitations. On a bus topology you are limited to the number of hosts you can place on a single bus. A ring topology can be beneficial because it provides redundancy, however …
Male or Female?
You may not know that many non-living things have a gender. For example: 1.) Ziploc Bags — They are Male, because they hold everything in, but you can see right through them. 2.) Copiers — They are Female, because once turned off, it takes a while to warm them up again. It”s an effective reproductive …